- cross-posted to:
- privacy@lemmy.world
- cross-posted to:
- privacy@lemmy.world
‘hacked’. Eh. There was an API endpoint left open that allowed them to basically just spam it with no rate limiting. They used the lack of a rate limit to just pull the data out of the API that it was made to produce.
Yeah. They got data in a way that was not intended. That’s a hack. It’s not always about subverting something by clickity-clacking like in the movies.
deleted by creator
Well…you son of a birch…now I’m in.
HTP.
Understanding that’s your reference, mine is that in Hackers they never said “I’m in” ;)
What about Sneakers? Or maybe The Net?
If it’s not in those surely it must have been in NCIS a few dozen times.
You name it, we got it!
Exploit. The system worked as intended, just without a rate limit. A hack would be relying on a vulnerability in the software to make it not function as programmed.
It’s the difference between finding a angle in a game world that causes your character to climb steeper than it should, vs rewriting memory locations to no-clip through everything. One causes the system to act in a way that it otherwise wouldn’t (SQL injections, etc) – the other, is using the system exactly as it was programmed.
Downloading videos from YouTube isn’t “Hacking” YouTube. Even though it’s using the API in a way it wasn’t intended. Right-clicking a webpage and viewing the source code isn’t hacking - even if the website you’re looking at doesn’t want you looking at the source.
Exploiting is hacking, quit being pedantic.
A system fault is not the same as a vulnerability. These would have different baseline CVSS 3.1 scores, with the temporal and environmental reducing over time. A medium/low at best for a public endpoint exposing PII.
deleted by creator
Hacking is the entire process including figuring out if something is or is not rare limited
A missing rate limit is a vulnerability, or a weakness, depending on the definition. You’re playing smart without having an idea of what you’re talking about. Here you go:
https://cwe.mitre.org/data/definitions/799.html
YouTube videos are public, and as such it’s not really hacking. If you were able to download private videos, for example, it would be a vulnerability like “Improper Access Control”. It does not matter in the least whether you use an “exploit” in your definition (which is wrong) or “just increment the video ID”.
The result is a breach of confidentiality, and as such this is to be classified as a “hack”.
Sure. Except you’re wrong and have absolutely idea of what people in this community say about things. Let me be a dick and literally googz this for you and find an embarassing answer because you couldn’t do it yourself.
So your googling proved him right. What’s embarrassing about being right?
They gained unauthorized access. From that guys definition that is a hack, no an exploit
But they are using a loophole to gain sensitive data. They did not gain unauthorised access to the system.
They absolutely gained unauthorized access to the data. Their access was not intended or sanctioned. If it was intended to be public and accessible like it was, this wouldn’t be a story and they wouldn’t have locked down the access.
With due respect, you are wrong.
hack
…
- (transitive, slang, computing) To hack into; to gain unauthorized access to (a computer system, e.g., a website, or network) by manipulating code
Hacking means gaining unauthorized access to a computer system by manipulating or exploiting its code.
Exactly what this is. Read the disclosure. What about your response doesn’t fit that?
They did not do it by manipulating code. This wasn’t the result of a code vulnerability. If you leave the door wide open with all your stuff out for the entire neighbourhood to see, you can’t claim you were “broken into”. Similarly, if you don’t secure your endpoints, you can’t claim you were “hacked”.
Lack of rate limiting is a code vulnerability if we are talking about an API endpoint.
Not that discussion makes any sense at all…
Also, “not securing” doesn’t mean much. Security is not a boolean. They probably have some controls, but they still have a gap in the lack of rate limiting.
It is a vulnerability, but exploiting that vulnerability is not generally considered by security experts to be “hacking” in the usual meaning of that term in academic settings. Using an open or exposed API, even one with a sign that says “don’t abuse me”, is generally not considered hacking.
I am a security professional. I would personally not care less to make the distinction, as both are very generic terms that are used very liberally in the industry.
So I don’t see any reason not to call this hacking. This was not an intended feature. It was a gap, which has been used to perform things that the application writer did not intended (not in this form). If fits with the definition of hacking as far as I can tell. In any case, this is not an academic discussion, it is a security advisory or an article that talks about it.
Well from a professional here: It is.
Please provide a link to whatever source claims this.
I hold a computer science degree and this contradicts the definition of “hack” versus “exploit” used in academic settings.
They probably typed it out themself then screenshotted it.
Hint – by manipulating or exploiting its code
Which I am explaining, they…did…not…do…
They did nothing to the code. They didn’t break the code, they didn’t cause the code to do anything it wasn’t designed to do. They did not exploit any code. They used an API endpoint that was in the open. For its intended purpose, to verify phone numbers. The api verified phone numbers, they verified phone numbers with the api. The only thing they did here…was they did verification on a lot of phone numbers.
They absolutely exploited unintended functionality. If this was intended, they wouldn’t have added rate limiting and locked down the api after. It was clear to say this was certainly not an intended use of the api.
In a video game for example, if there is a an item that caused excessive lagging just by placing the item. Placing a lot of them with the intent to lag the game would be an exploit. They only used items sanctioned by the game, but for unintended reasons and they would likely be banned for exploitation.
You’re arguing with someone who was agreeing with you 😑
You are correct, I replied to the wrong comment
That’s what most exploit-based hacks are. A developer makes a dumb mistake and then someone exploits it to do something they shouldn’t be able to do.
This isn’t about being pedantic but sure, mate.
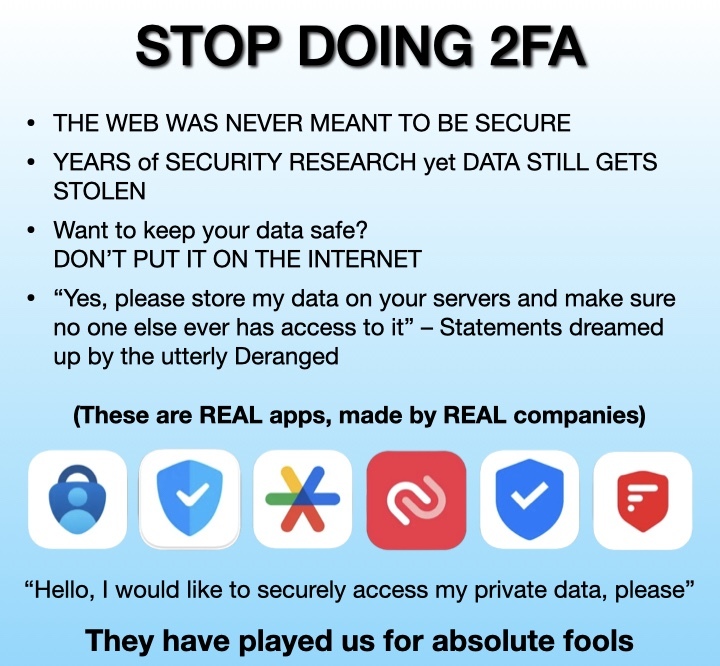
Companies need to stop using Authy. It’s stupid and pointless when we have a open alternative such as the one used by Google Authenticator or Aegis.
I started using Authy instead of GA because every time I changed the ROM on my phone I would lose all codes, because I would forget every time.
Use aegis, export the keys and then reimport them every time you switch. Trusting your second factor to a cloud is a disaster waiting to happen.
If you want to get fancy setup your own cloud server (nextcloud, Seafile, owncloud etc) and set the backup folder for aegis to the self hosted cloud for easy restore every time you switch ROMs.
Simpler approach: auto export from aegis when an update occurs, syncthing or similar to your home PC. I have it synced across several computer in different locations and aegis is good enough to make unique filenames, combine with syncthing file history and I’m good for like 2 years of backups.
GA now backups your codes in your Google account, so this doesn’t happen anymore.
They had an obvious solution which is export to an encrypted text files and went with the option that lowers your security
Google usually goes with the lowest common denominator solution. There is a staggering amount of people who don’t know what is a file, let alone that phones have any.
This isn’t about you and your silly follies
I’ve started putting mine into my Bitwarden vault as well as Google auth, mainly because I’m a bit paranoid I’ll wind up locked out of something by trusting a second factor too much
With password recovery you shouldn’t be getting locked out of anything. I don’t see this being a risk.
Password recovery is itself a weakness in the system
And I did call myself paranoid for it…
Call my job and tell them this please. I have to use this shite everyday and it sucks.
I expect most usage of authy was based on the open TOTP protocol that Google etc use. The additional benefit was backing up those codes to the authy account, hence the avenue of attack on those accounts.
I agree though, Authy, especially since it was bought out, should be avoided. They deprecated their desktop app which was the only semi useful part of their suite, but I stopped using it years ago.
You know it’s bad when people recommend something made by Google over it.
Red Shazam
Wow, it’s literally the shazam logo, flipped horizontally and red.
Wonder who got paid to make that logo?
Intern
So, nobody got paid to make that.
I realized long time ago that I don’t want my 2FA be tied to my phone number. And then i found you can’t export your data from Authy because they know they are scummy fucks and don’t want to anyone to leave
You can, though. But not through their app. Someone reverse engineered their protocol and wrote a program that connects like a new client, which you then approve, and it dumps all your random seeds into a text file. I then put them all into Keepass.
Edit: Unfortunately, the author has deprecated the project as Authy has added some attestations to their API, seemingly for this exact issue. https://github.com/alexzorin/authy?tab=readme-ov-file
deleted by creator
Remind me to start a batch rekeying service.
deleted by creator
If there’s a benefit to such a tool would bad actors have already developed one?
They got rid of the desktop app.
Also, with shouldn’t have your seeds. They’re encrypted before they are transmitted to their servers and only decrypted on the device.
Do you know what it’s called? I’d like to do this if possible.
They added a link, but the project has been deprecated
So what did you do?
On Android, I replaced Authy with the open-source Aegis app. It’s just as functional, allows exporting, and doesn’t tie your data to your phone number (nor store it on a central system–not sure if Authy does this or not).
Use TOTP wherever possible. It’s standardized, and typically can be found somewhere if you keep digging hard enough.
Plenty of services push their own proprietary systems hard though. Looking at you M$
I also find this infuriating. I had a service offer TOTP for authentication. Installed an open source TOTP Aap, scanned the QR and voila.
The service meanwhile can control whether they want to generate a new token or give out the old one again, for instance when a device was lost.
It is the most easy, most convenient solution both for the service provider and the client. There is no excuse for any other 2FA system to be used.
then i found you can’t export your data from Authy
Exporting data from a 2FA app sounds like the opposite of secure. Not to mention you don’t want your 2FA codes on Authy (or any other 2FA app) to remain valid if you’re not using it.
When I switched from Google Authenticator to Authy years ago, I went through each 2FA-enabled account one by one to disable 2FA and then re-enable it using Authy. It’s a long process depending on how many accounts you have 2FA enabled on, but it’s worth it.
Reading the OP, looks like it’s time to generate new keys for all my 2FA accounts.
If you can’t export / save / transfer codes then you need to regenerate all your 2fa codes every time you switch to a new device.
2FA doesn’t need to be infallible, it just needs to be a second factor.
I used this method to export my twitch 2FA to Aegis. although I did this a few years ago, I think it still worksEdit: reading though comments made me realise Authy’s desktop app doesnt seem to be a thing anymore, so sadly I dont think it works anymore
Wow, that was one of the things that drew it to me in the first place. I break phones too frequently to feel comfortable leaving everything to them.
deleted by creator
Bitwarden would be my vote
I’ve been running a self-hosted Vaultwarden server with Bitwarden clients. It’s been perfect. The clients could use some usability work, but other than that, no complaints.
Just out of curiosity: is it wise to keep you MFA within your password safe? Like is that not the opposite of multi factor? I’m no troll, I’m seriously uninformed.
Realistically the threat we care about is others leak your password. So it doesn’t matter.
If you have a setup where your password vault is at risk then yes it’s a bad idea.
I suppose there is a certain level of risk but that’s true with any solution. Passwords generally don’t get changed very often and that’s usually what’s going to be nabbed up by somebody that in your username of course. With TOTP, putting that in bitwarden means that in order to get access to whatever account, they first have to get your credentials which they probably got from a dump filled with a bunch of other credentials, then I’d have to figure out that you’re using bitwarden was your be no sign that you are. Then they’d have to actually get into your bitwarden which if you’re doing it properly should be difficult. And if the login to bitwarden is completely different than the account are trying to get into it’s basically invisible to them.
The only way I see bitwarden being the weak link, is 1. Someone has physical access to your devices and they know what they’re looking for (in this case it’s probably a roommate or family or friend, someone that you trust but probably shouldn’t). 2. Bitwarden gets compromised (which is an impossible but it is probably more difficult because it is an open source thing). 3. You go to shady website and install shady stuff and that install some sort of keylogger, or something else that shows what your system has (hell, Microsoft recall would actually fall into this category) and a back actor sees that you have bitwarden and how you log into it. But that being said, 1 and 3 aren’t necessarily stopped by having a password manager solution and the separate MFA solution… But it could slow them down.
But physical MFA isn’t impervious either. I don’t recall if it was yubiki or Google’s Titan, if I remember back years ago one of them had a problem.
This
Aegis
These are not local solutions, but are cross-platform and open source: Bitwarden or Proton Pass.
Doesn’t synced solutions completely defeat the purpose of MFA?
Not if you protect the master key with MFA, like a yubikey. Then it’s cryptographically secure for quite a while…at least until quantum computing is affordable enough to be used against your data. Or the database and your yubikey and yourbpassphrase are compromised
You’ve got a good point. I wonder if this an example of a trade-off between convenience and security. If you’re logging in and you get an MFA prompt, a Yubikey has to be physically searched, while Bitwarden or Proton Pass only have to be clicked. A Yubikey can only hold a limited amount of accounts, while Bitwarden or Proton Pass could hold many more. Of course, a Yubikey could be used as MFA for Bitwarden or Proton Pass, but that would create a single point of failure and reduce factor separation (which I think is your original point).
While I posted a Bitwarden or Proton Pass recommendation of sorts, I genuinely wonder if it’s advisable to not use MFA at all if the factors will not be separated. Or, perhaps, the best security solution is the one you’ll actually use. I guess the answer is the good ol’ “What’s your security model?”
I wonder if this an example of a trade-off between convenience and security.
I genuinely wonder if it’s advisable to not use MFA at all if the factors will not be separated. Or, perhaps, the best security solution is the one you’ll actually use
Your first and last statements are correct. Using your password manager as your MFA is a trade off with security and convenience, but that added convenience helps make it more usable so you actually use it. Anything is a trade up for most peoples’ awful password hygiene, so the trade off is worth it in my opinion.
Regarding the advisability of combining password and MFA into one platform: while you are lowering the overall security of your accounts, if you secure the main account with a long/strong password and a hardware security key, I would say that’s still more secure than not having 2FA enabled or not using secure passwords.
I like 1Password’s built in MFA support, if it’s a really sensitive account I use Google Authenticator because I haven’t bothered researching better local alternative
Edit: Going to try Aegis for the more sensitive logins, looks like what I’m looking for
You are not any more secure with google authenticator for 2fa, are you?
Possibly not now that it saves your codes to your google account (it didn’t use to), but it made me uncomfortable for my password manager to have both factors together to log into something like my bank or root AWS account. So you’d have to compromise two different places to get in
Most KeePass clones have it now, i use Keepass2Android plus KeePassX on PC
Most decent password managers (e.g. 1Password, Proton Pass) have MFA built-in. Use those.
https://news.itsfoss.com/ente-auth/
I use this on my windows machines, offline , has biometrics, supports export and import from aegis. Is new and untested but past few months have been solid.
I’d recommend 2FAS Auth
Yup it’s pretty good, although I would’ve liked it better if they provided a good way to export the data to another app
Technically they export a json file (with a different extension). But you can move to another tool with this.
deleted by creator
It’s good
USB keys. Good luck getting one of those hacked.
To be more concrete: security keys can communicate over USB or NFC. Just make sure it supports the protocol you want to use it for.
But there is also passkeys which is both software- and hardware based and is almost equally secure.
Buy a few (at least 2 for a backup) yubikeys.
Much more secure.
You can store the TOPT codes on them, but then you can also do all the higher security things too.
No one’s breaking into your Google account if you secure it with those keys and remove the sms backup method unless they’ve physically stolen the yubikey
KeePassXC does have this functionality on desktop as well as on SOME android apps (no idea for iOS). For android I like KeePass2Android Offline, iirc it was recommended on the official KeePassXC website (you may want to check it out).
deleted by creator
lol. I am glad I became privacy conscious before this happened.
did they have 2fa on?
Of course. It was on the office phone that gets passed around to whichever tech is on call. The on-call tech left it at Mcdonalds accidentally.
welp
Deleted my Authy account, Thankfully I only had indeed and humble bundle attached.
What do you use now?
Check out Aegis if you’re on Android. (See my other comment).
Use google authenticator
I’d honestly be very cautious with anything google. Aegis would probably be a better option.
Does it work for Android?
Yep! Using it on Android rn.
Does anyone have a suggested alternative for authy? (Please read the whole post before responding)
I’d love to go with an open source solution as I’ve done with my password manager, but that doesn’t seem possible with one of my big requirements:
Scenario: I’ve had my phone robbed abroad and managed to buy a new one and loaded my ESIM back into it—I need to recover access to my 2 factor database via SMS so I’m able to log into my cloud storage and access my password database.
At this point I’d probably be happy to host a service myself on something like AWS and use SNS for this requirement, but I’m not sure anything like that exists ready to go. I’m not particularly interested in rolling something myself for this.
I’d be dubious of jumping from one closed source product to another, but if there’s a particularly good option I’m all ears, I’ve been otherwise happy with authy for about a decade now, but this plus the retirement of the desktop app have me looking elsewhere.
Edit: added emphasis
I use Aegis, which I periodically back up manually off phone.
(reposted from another comment mentioning aegis)
Interesting, I’ve seen this one before but it didn’t seem like it would support my deal-breaker scenario—I still can’t seem to see support for that on the readme, could you point me at some docs?
I think the suggestion here is to back up Aegis. I do something similar using Aegis + SyncThing.
I have a folder on my phone that is synced with my PC. Every so often, I will back up Aegis to that folder, and then it automatically syncs to PC.
Oh, in that case it’s not quite equivalent, because my cloud storage is protected by the two factor code stored in my Authy OTP database.
I would still need to access the OTP database before I could access the cloud storage, which is where it would be stored in this scenario.
Forget your existing cloud. Your 2FA backup doesn’t need to be protected by 2FA; just encryption and a strong/unique passphrase. Your 2FA backup can’t be used to access any account on its own, without each password. Most OSS E2EE services allow you to create a free account; many without an email. Pick 2 for redundancy, create a NEW account, and set a NEW passphrase (like your 2nd “master” password). Before you transit upload your OTP backup to both of them.
This approach is probably more secure than SMS to access 2FA, especially vs a closed source provider like Authy, and especially if your 2FA export is also encrypted with a different password. If you’re already using a password manager and unique passwords for everything, you’re already 95% more secure than everyone else, and removed the primary need for 2FA (password reuse and theft). If you’re doing everything else right, 2FA only makes you 5-10% more secure, and covers far less-likely threats (email takeover, MITM, etc). Sys admins have been raw dogging SSH and PGP keys every day without a 2nd factor, for decades.
Sames, aegis ftw
Bitwarden has 2FA built in, and you can host it yourself if you want.
I’ve looked into this before and unfortunately it doesn’t support the SMS requirement I have in my deal-breaker scenario—do you know if this has changed and can point me to the docs regarding it?
Oops, missed that part. Not that I know of, though SMS is a terrible way to do 2FA. It annoys me so many businesses and banks use it.
I agree it’s much worse than using a modern OTP app, but I need a way to access my OTP database when the only form of digital identity I have access to is my phone number.
Authy currently supports this scenario for me (with a load of checks, it doesn’t happen instantly), so I would require a like for like replacement
Bitwarden has a 2FA recovery code possible so you could use a unlabeled hard copy of the code. It cycles after every use so it would get you one recovery and doesn’t use SMS so it’s immune to SMS shenanigans.
That’s potentially a solution then, as I guess in order to buy a new phone I would need to have not lost my wallet too at least, so I guess I could keep those items together for equivalent recovery possibility
Okay that may be a goer, I’ll look a bit more into it, thanks!
Do you really need that ?
Self hosting means you have outside your phone your real vault and the phone is just connecting to it to refresh its local data.
I’ve setup my vaulwarden in my local network kit’s the local bitwarden server i use), my phone, tablet or simple webbrowser can connect to it when i’m home via the classic bitwarden (with self hosting parameters).
If i travel, i have just to start my openVpn session and connect to my home but it’s only needed if I want to update something (the encrypted cache it’s enough for consulation). If I have nothing to change, no need to have a vpn. I just use the cached data.
If my phone is stolen the data are safe (cache is encrypted, source is not on the phone). I revoke the vpn access by precaution and move one. No sms scenario needed here.
You only need to have a backup phone or computer to setup your new access on the new phone.
Edit: of course my vpn connection is protected by a passphrase so nobody can connect to my home network without me around. And the bitwarden app is also protected of course.
Do you have a second factor for your VPN? Or is it literally just a passphrase and you’re in? I also need a shared key to access mine, which puts new back at square one (I will not compromise on this)
I do really need what I’ve described because it’s literally a situation I’ve been in.
passphrase yes. It’s a long sentence than only me know.
As i use this vpn only when travelling and the passphrase doesn’t change, i can use my phone or tablet cached data to get the passphrase if i forget it.
And once connected to my home network via my vpn, i have access to all my services (vaultwarden, jellyfin, storage, etc…). All require of course login as i’m not accessing them from my local network.
If you self host vaultwarden you won’t have an SMS backup, but provided you need the code to login to something online, you can log into Vaultwarden from anywhere with an internet connection.
Aegis is often recommended as an open source solution : https://github.com/beemdevelopment/Aegis
Interesting, I’ve seen this one before but it didn’t seem like it would support my deal-breaker scenario—I still can’t seem to see support for that on the readme, could you point me at some docs?
The point is you physically and locally back up the database. Put it on your computer, or a flash drive or whatever. You can set a different, longer password for backups, and I would recommend you do that. When you get your new phone, you just copy the database into it and load it into a freshly installed Aegis. You don’t even need to self host anything, there is nothing to host.
Not everything needs to be “in the cloud”. I think this event illustrates nicely why.
This is specifically a scenario where I’m starting from a single blank device because I’ve just been robbed on the other side of the planet.
Edit: for added weight, I’ve been in this exact scenario. I was able to get my ESIM reprovisioned to a new phone and recover everything within a day. I don’t want to replace authy with a solution that doesn’t cover that scenario
Well I thought this was kinda obvious what I meant, but I guess not. What you say is a requirement (sms recovery of a cloud account) is just one of many solutions to your specific problem. I’ll just list off a few solutions below that involve neither SMS (the most insecure communication method in common use today) and only optionally a cloud account. For cimplicity sake I’ll stick to Aegis, where you can create password-protected local backups you can then put wherever you want. This password needs to be very strong for obvious reasons: I would recommend a long sentence (40 characters or more) that you can just remember, like a quote from a movie/tv show/book/poem or something, including normal punctuation as a sentence for example.
Solution 0: This is more of a trivial solution I wouldn’t actually recommend. You can allow account recovery via eMail and have your eMail not use 2fa, but a long/good password so you can login from memory (see above). This is probably more secure than SMS for the recovery-case, but less secure for the everyday use case of eMail, therefore “not recommended”.
Solution 1: USB Sticks are tiny, as in the size of a USB port (slightly longer but slimmer for USB-C). If you want to have a backup “on you”, I’m sure you can find a place where it wouldn’t get robbed with the phone/wallet. A tiny pocket somewhere, a string around your ankle, make a compartment in your shoe, or just have it with your luggage at the hotel. I’m sure you get the point. You get your new phone, you plug in the USB, you install Aegis and restore the backup.
Solution 2a: Dedicated “online” storage. This can be self hosted, or a free account of any cloud provider, but the important part is that it does NOT require 2FA and you do NOT use it for anything else. You have the backup in there. It also needs a very secure password (again: long, but easy to remember, no garbled letter nonsense), but obviously not the same as the Aegis-Backup. So you now need to remember 2 long passwords. You get your new phone, you log in, get the backup and proceed as usual.
Solution 2b: If not having 2FA is not an option for the solution above, you can have a friend/family store the 2FA on his phone. To log in, you go to the login page and enter your password (which your friend doesn’t need to know), and you ask him over the phone for the current 2FA-Code, which he tells you and you can log in, download the backup and proceed as above. I assume such a high security isn’t that critical, since you have been using something involving SMS. Restore then goes as per usual.
Solution 3: Store the whole backup with a friend and when you need it he just temporarily puts it somwhere you can access, and removes it again after. Since the backup is protected by a monster of a password, and the accessibility is temporary anyway, this isn’t security critical.
Solution 4: If you absolutely must, you can find a cloud-provider for 2FA, and use it only as the “first stage”. The only 2FA code in there is the one you need to get access to your main online storage/account where you then have your real Aegis-Backup and/or other files. Obviously this service would need to allow you to login without 2FA, and the usual password rules resulting fom that apply. You can just add the 2FA of your primary service to more than 1 app or service, or if it allows for this, you can generate multiple authenticators so you can also revoke them serperately if needed.
Well I thought this was kinda obvious what I meant, but I guess not.
Alright, drop the sass, if it was obvious your post wouldn’t be the length it is. Now chill, I genuinely appreciate your response
0, no go
1, also a no go, I can’t guarantee I’ll have an extra thing
2a. No 2fa, so this is a reduction in my current security
2b, this could be workable, I already self-host a number of services, but I want to be sure situational neglect (i.e. life is too busy for me to pay attention) cannot compromise this, therefore it’s gotta be a turnkey solution that I can configure to auto update, which is what I’m asking for in my comment. I need your specific solution for this, generalisms are useless here.
3: Not workable, I can’t rely on someone else being able to help in every possible scenario (and tbh I wouldn’t want to put that responsibility on someone)
4: This is a pretty good one tbh, though I guess if I’m going to pick holes, if the first stage is good enough as the gate, it diminishes the reason to have the second stage, so I’d wonder what you would suggest that could tick all the boxes for that first gate.
Edit: weird numbering formatting to combat lemmy formatting doing weird things
2a. No 2fa, so this is a reduction in my current security
That’s open to interpretation. Your current solution you thought was secure, but you used a service that as it turned out had bad security practices, which you just didn’t know (arguably couldn’t know). ANY online/cloud service that you don’t host yourself has this issue with being a black box of unkown quality. Any online service you do host has to be secured by you (or you need to trust that the base setup of that tool is “sufficiently secure”), and is in essence limited by your knowledge of the tool and technology used. Also if you’re reusing any passwords, anywhere, just stopping that practice is likely more secure in practice compared to 2fa in isolation.
2fa in general isn’t just plaing “better” than not having it, security is rarely this black and white. It also depends on what is allowed to be the “second factor”, and since yours included SMS, it really wasn’t secure at all (like others have also mentioned in this thread). And it depends on the password of course. For example if you use a really secure password (30+ characters), and don’t reuse it, it will in practice be more secure than a short(ish) password and a 2nd factor that allows SMS. Generally 2 factor is used as a term for 2 categorically different athentication methods: one thing you know (password, pin) and one thing you own (phone, physical device/key, or a file works too). The problem is that SMS doesn’t require your phone. It’s incredibly easy to get the SMS without having your phone (even easier with physical proximity) or flat out faking owning your phone number (dpends on a lot of factors how easy or hard that is in practice, doesn’t require physical proximity). Basically, if someone actively targets you and/or that account secured by SMS 2fa, it isn’t overly hard, but it’s good enough at preventing giving access through a data leak for example.
So, back to the security of “solution 2a”: how would someone get access to a long password you don’t use anywhere else, that isn’t written down anywhere (or nowhere accessible), and where you essentially never need to use/access the account in the first place? Nobody would even know that whole account exists unless you specifically tell them, let alone knowing how to get in. Note that this can also be combined with the concept in solution 4, so you’re then using it to only restore a single 2fa code. So that “safety net fallback account” very rarely needs to be updated with a newer Aegis-Backup, making it even more obscure/unknown. That 2fa code then lets you access your normal account and backups, and you restore the full suite of 2fa you need.
It boils down to this: local 2fa with a backup means you need to get access to a single file to securely restore full access to everything. That file can be transmitted insecurely (due to strong cryptography and hopefully a good password not used anywhere else), but I wouldn’t store it out in the open either. On the other hand, any cloud based solution is an inherent black box. You trust them to properly do things, and you only know they didn’t once it’s too late (like Authy). It also means they are, by nature of what they do (storing account access information), a target and if the attacker is successful, you’re the collateral without having been explicitly targeted. Maybe there are sevices out there that let third parties audit their security and publish the results, but I don’t know of any and it would probably increase the price by an prohibitive amount for most people.
What I do is using synching to sync my files on my PC when I am at home. You could also manually back it up on a cloud drive.
Anyway I think it’s best practice to store somewhere recovery codes.
Do you carry your recovery codes with you at all times?
I guess I could do this, but it seems like a downgrade from my current situation
If you’re talking about being able to regain access with no local backups (even just a USB key sewn into your clothing) your going to need to think carefully about the implications if someone else gets hold of your phone, or hijacks your number. Anything you can do to recover from the scenario is a way an attacker can gain access. Attempting to secure this via SMS is going to ne woefully insecure.
That being said, there are a couple of approaches you could consider. One option is to put an encrypted backup on an sftp server or similar and remember the login and passwords, another would be to have a trusted party, say a family member or very close friend, hold the emergency codes for access to your authentication account or backup site.
Storing a backup somewhere is a reasonable approach if you are careful about how you secure it and consider if it meets your threat model. The backup doesn’t need to contain all your credentials, just enough to regain access to your actual password vault, so it doesn’t need to be updated often, unless that access changes. I would suggest either an export from your authentication app, a copy of the emergency codes, or a text file with the relevant details. Encrypt this with
gpgsymmetric encryption so you don’t have to worry about a key file, and use a long, complex, but reconstructable passphrase. By this I mean a passphrase you remember how to derive, rather than trying to remember a high entropy string directly, so something like the second letter of each word of a phrase that means something to you, a series of digits that are relevant to you, maybe the digits from your first friend’s address or something similarly pseudo random, then another phrase. The result is long enough to have enough entropy to be secure, and you’ll remember how to generate it more readily than remembering the phrase itself. It needs to be strong as once an adversary has a copy of the file they jave as long as they want to decrypt it. Once encrypted, upload it to a reliable storage location that you can access with just a username and password. Now you need to memorize the storage location, username, password and decryption passphrase generator, but you can recover even to a new phone.The second option is to generate the emergency, or backup, codes to your authentication account, or the storage you sync it to, and have someone you trust keep them, only to be revealed if you contact them and they’re sure it’s you. To be more secure, split each code into two halves and have each held by a different person.
I have similar requirements to you and honestly the best solution I could find was Microsoft Authenticator. I know Microsoft bad etc, but if you already have a Microsoft account anyway you can back up all your 2fa codes to your iCloud or Google account. If anyone knows of an open source alternative I’d be interested, but the ability to recover my accounts is more important than using something open source
2FAS
This. Superior in any way to authy.
This is a new one to me, but a quick look at their homepage doesn’t seem to suggest SMS support as per my deal-breaker scenario—could you point me to the docs describing that functionality?
Aegis. Make an encrypted backup. Store the backup safely. Done
I highly recommend 1Password. It’s cross platform, including Linux, and it’s not only a great and sort l super secure password manager, but it also does 2FA codes and if you use their auto fill tool, it will also paste the 2FA code to clipboard so you can paste it in seamlessly.
Everything is full encrypted and needs a really long, unique to you, key to decrypt. So no one will be hacking this anytime soon. Even 1Password cannot open your vault.
Like many others in this thread I love Aegis, I regularly back it up to my nas and it hasn’t failed me yet, but I also selfhost Vaultwarden. Recently I’ve found myself copying a lot of my secrets over so if I don’t have my phone, I still have a way to use TOTP.
Ente auth is new, but open and cross-plat, unlike aegis. Aegis still wins on Android but ente can import aegis encrypted backups.
I use Aegis
I left Authy a couple of years ago when I realized that I can own my own data. I use KeepassXC. For sync, just syncthing. Both free and I 100 % control of it.
Any online password manager is in my opinion is stupid as it will sooner or later get hacked - info leak. Some may not even apply zero-knowledge about the passwords.
This is why I switched to Bitwarden, will probably move it to self hosted at some point as well
Why does it require a phone number to use?!
They wanted to let companies pay for a non standard 2fa code generation tied to the phone number as it was easier than the mainstream option that was the almost abandoned google authenticator that didn’t allow backups.
Cloudflare, humble bundle used that scheme and I hated them for that. Seems that now that plan failed and essentially now authy is a money-losing operation for twilio and this shows on the unsecured API access that allowed the hack
Also, Google Authenticator now supports backup. Aegis is another free alternative.
And as soon as I learned about that I stopped using it. Turns out it was the right choice - since then more then one company had breaches where authenticator seeds extracted from a google account were used to bypass 2fa.
It’s completely optional to connect a Google account. You can always back them up using the QR code (just take a picture with another device)
deleted by creator
Friendly reminder to change your master password. You’re one SIM jack away from having your life locked away for ransom. They didn’t breach the seeds, but next time who knows. I would start migrating and changing 2FA codes just in case. You never know who might be spraying.
The problem is so many services requiring SMS to be that second factor. From what I’ve heard it’s easy enough to steal a sim that if you’re being explicitly targeted it’s basically the same as no second factor. Yet even if using an authenticator app most services require you to still have SMS/phone as another option for the 2FA.
For Authy specifically they’d need to guess your master password and then hijack your phone number, and for users of Authy I suspect their passwords are not easily guessed as it’s already a step above the standard SMS only 2FA most services require.
Stop. Trusting. Cloud/SAAS. Security. Apps.
Don’t give them your passwords and private keys, because you can never know of they’re being stored responsibly, or who has access to them.
Don’t give them your personal details, they don’t care about protecting user anonymity.
Keep your keys and passwords in local, encrypted files, and generate your TOTPs locally.
“But that’s not convenient!” - It’s plenty convenient, find an app that supports your phone’s biometrics. There are plenty on both Android and iPhone that also work in Windows/MacOS/Linux.
“What if I lose my phone?” - Keep your files backed up. If you don’t do this, you deserve to get locked out. Fear of losing data is a good thing, it keeps you vigilant. Apathy gets you another of these stories.
There are plenty of apps that encrypt local storage for security keys and code generation. Stop allowing these tech bros to create
honeypotscatnip for hackers, and making you pay them for the privilege of being an easy target.Edit: I’ve been using “honeypot” wrong. It would actually be good if the hackers tried to hack one of those.
“What if I lose my phone?”
I’ve referenced this scenario in a comment elsewhere in the thread. You’ve missed the problem in your solution.
A backup is useless if I can’t access it when I need to. In the scenario where I’m far from home and have only got a replacement phone to work with, I need a way to access my OTP database (with only my phone number as a 2nd factor, thanks to ESIM provisioning) so I can get to my cloud storage for my password database.
This is a real scenario that doesn’t seem covered by most options and people seem to keep glossing over it (And before anyone says that’s not likely, I’ve been in that exact scenario before)
Who said you shouldn’t be able to access your backups remotely?
A lot of tools allow you to set up google drive, drop box, whatever. Yes, this brings you back to cloud, but it’s better to have a hacker wonder if some random google drive might have juicy auth data than know for sure that some SaaS platform absolutely does. Also, even if they got the file, it should be encrypted, and should be a massive pain to get into (at least long enough to change the passwords stored in the file).
The other (better) option is to have it back up to sftp (or similar), which you manage yourself on private servers. Normally this would be accessed through RSA and/or TOTP, but you can set up secure backup methods (combo any/all of; port knocking, long-password, human-knowable timed password, biometrics, security questions, other trusted humans that have some TOTP that can’t open your storage alone, etc).
Right, I get that and that would 100% be part of the solution, but I’m not going to have my cloud storage protected only by a single factor.
Specifically I’ve kinda happily landed on Authy’s SMS being the 2nd factor in that scenario (and that scenario alone as it’s generally one of the worst 2nd factors) because I know I can get my ESIM reprovisioned with a phone call to my provider. Plus Authy won’t just give me access with an SMS alone, there are verification steps before they will let me access it, which adds piece of mind given the reduced security of an SMS OTP.
I’m not interested in cobbling together my own “secure” solution, I would happily host something ready to go (seems like bitwarden might be a front runner here), but I’m not going to trust my glue is perfect if I’ve had to do much more than pull a container and set-up a reverse proxy. I cannot guarantee I have the time to patch vulnerabilities manually, etc.
Whoa there, I never have - and never would - suggest that anything should be protected by a single factor. Where are you getting that?
Authy sucks. It’s not just that the TOTP they send you might not be secure (SMS is easily exploited), it’s been shown that they’re leaking other personal data.
You don’t have to cobble anything together. As you say, self-hosted BitWarden is a good option. As for your “glue”, you should trust it more than a third party, since you know what went into yours, and its not a massive
honeypottreasure trove.Edit: I’ve been using “honeypot” wrong. It would actually be good if the hackers tried to hack one of those.
Syncthing across all of your devices. Use your desktop or other home PC to sync to a secure cloud service using rsync or freefilesync on a schedule. If you know all the words I just said it’s like an hour of work, if not it’s probably 4-6 (piecemeal, not a block).
deleted by creator
Weren’t they hacked last time? Is this old news or a new hack they never learned from?