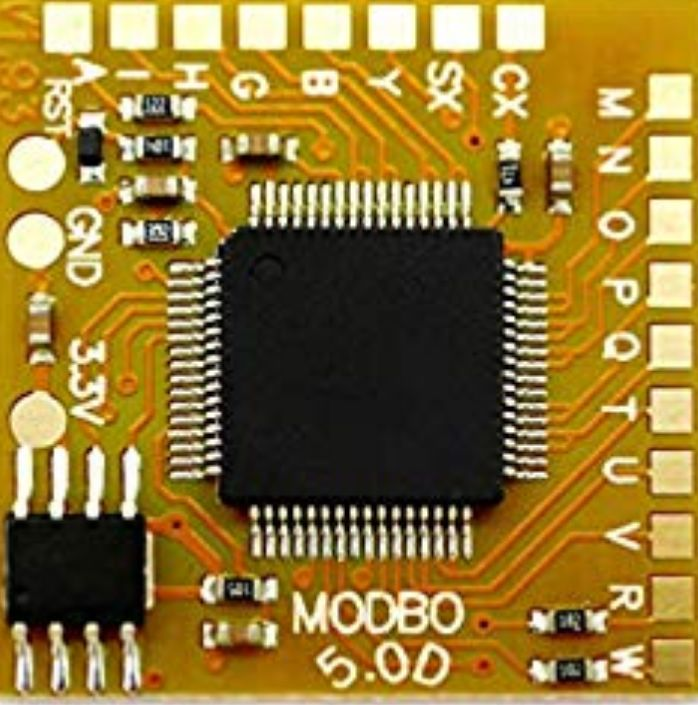
The Sony PlayStation 2 contains a chip called MechaCon. Its job was to be the system’s ultimate security gatekeeper, controlling disc authentication, region locking, MagicGate encryption, and KELF file decryption. For years, it was considered the last unbreakable barrier in PS2 security. Modchips could only bypass it. But buried inside Sony’s redesigned Dragon MechaCon it was discovered that it was EEPROM patchable and exists a factory service feature.
In this video take a closer look at the exploit chain from the PS2’s boot certification handshake through the cryptographic failures, and the tools that finally cracked it open: MechaDump and MechaPwn. The factory backdoor Sony built for their own service centers became the front door for the homebrew community.


I didn’t realize the MechaCon chip handled so many security layers on the PS2 — it’s crazy how central it was to authentication and region locking. The fact that a factory service feature became the key to bypassing it is such an unexpected twist. Tools like MechaDump and MechaPwn really show how deep people went to understand the system. The technical breakdown made it easy to follow even if the topic is complex. The pink background in the video also makes it visually clean and easier to watch.